The process to launch a firewall within the Rapid Access Cloud is simple and easy to perform. After the initial technical meeting, you will confirm with your firewall vendor the type of firewall to purchase.
Once you obtain the license from the firewall vendor, the VFS team at Cybera will build the backend needed for you to launch and operate your virtual firewall instance. Here is an overview of what the VFS team does prior to launch:
Horizon is the graphical user interface of OpenStack, which allows you to interact with VFS on the Rapid Access Cloud, provided by Cybera.
The interface is fairly simple to use. Typically you will only use the "Compute" tab, from where you will launch and destroy instances.
In this wiki, Rapid Access Cloud dashboard refers to the Horizon interface.
Within the Rapid Access Cloud, there is a selection of Flavors and Images that can be accessed:
In the Rapid Access Cloud, you will have your own flavor and image, depending on the firewall vendor chosen:
For example an f1.medium instance indicates a medium Palo Alto instance and an f2.large instance indicates a large Fortinet instance.
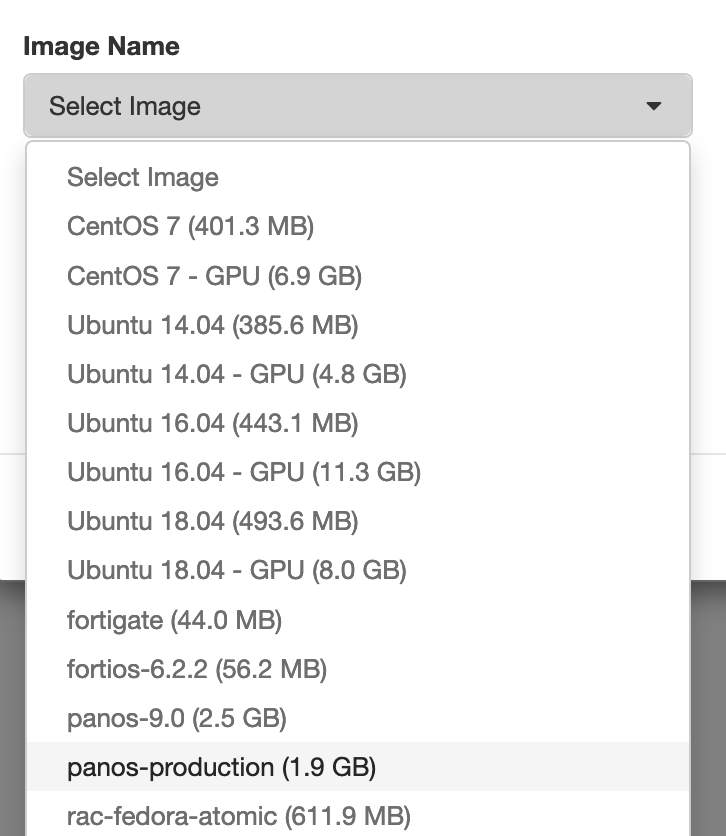
You will be granted the appropriate image during on-boarding, based on the choice of firewall.
Please review this link for the list of firewall images currently available on RAC from the vendors we support.
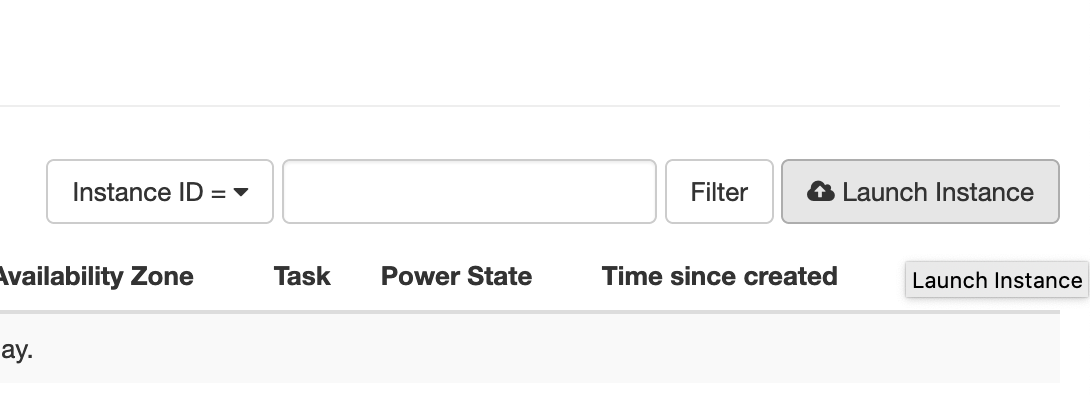
The Rapid Access Cloud dashboard is the primary means of maintaining a VFS instance. With your Rapid Access account in place (see here to create an account) and the backend work completed by the Cybera VFS team, the steps below show how to launch a VFS instance from the Horizon dashboard.
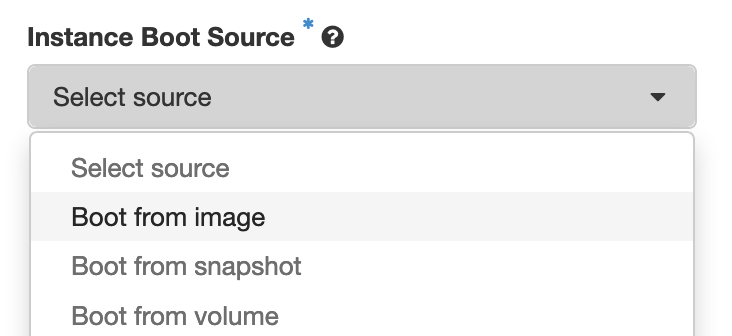
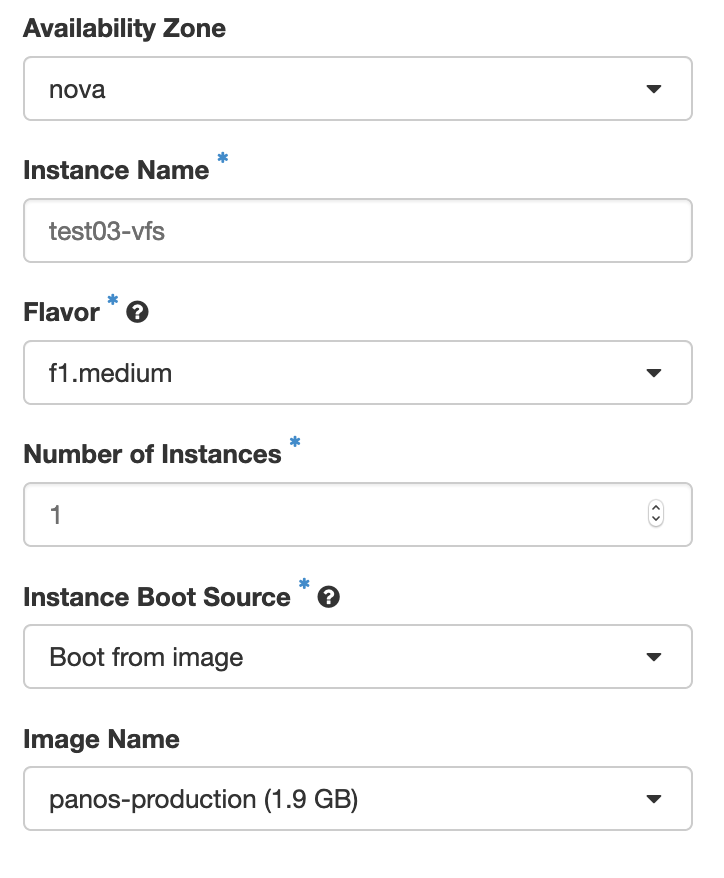
Give the instance a name, and choose the appropriate flavor. Depending on the virtual firewall of your choice, the corresponding flavor should be chosen for the instance. See the table below to identify the right flavor for your virtual firewall:
| Palo Alto Firewall | Flavor | Fortigate Firewall | Flavor |
|---|---|---|---|
| VM-100 | f1.small | VM-02 | f2.small |
| VM-300 | f1.medium | VM-04 | f2.medium |
| VM-500 | f1.large | VM-08 | f2.large |
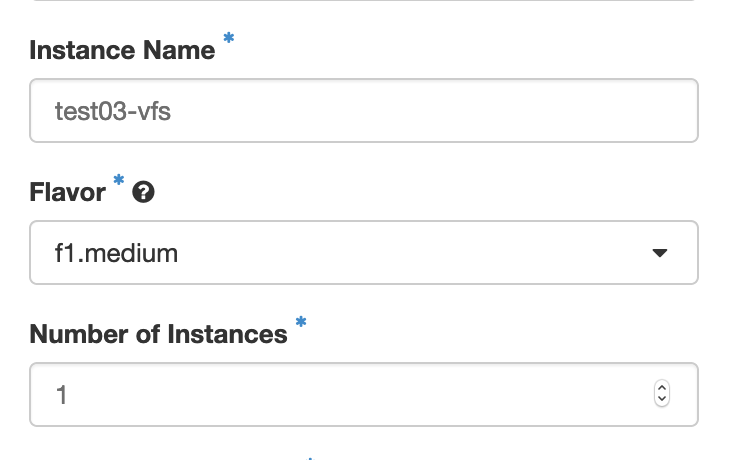
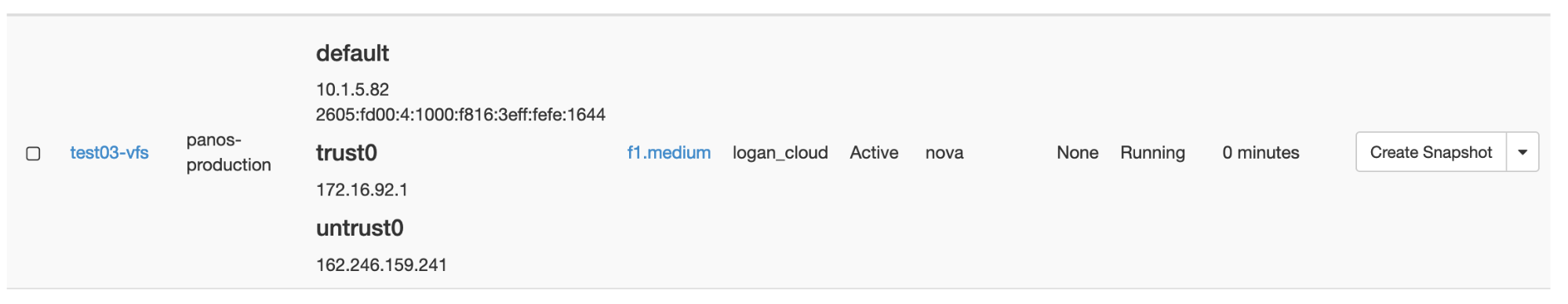
In the example above, the name test03-vfs has been given to the instance, and the flavor (f1.medium) indicates it is a Palo Alto instance.
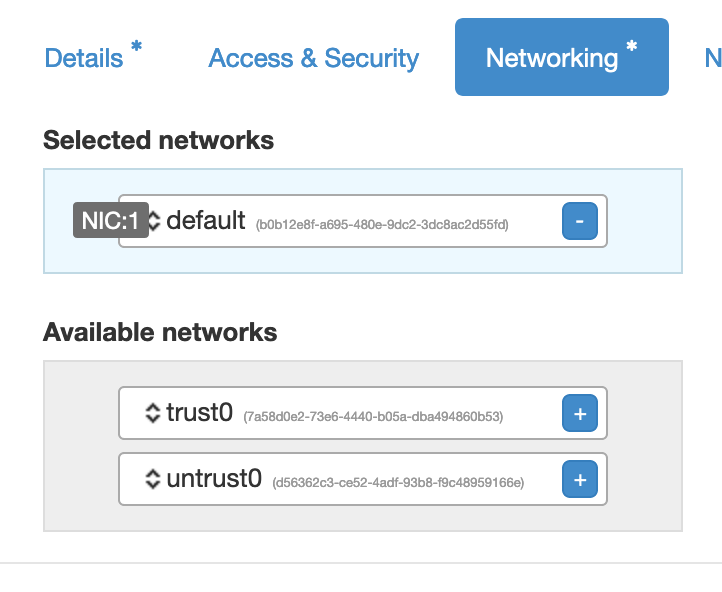
Under “Network Ports” tab, check both trust0_port and untrust0_port: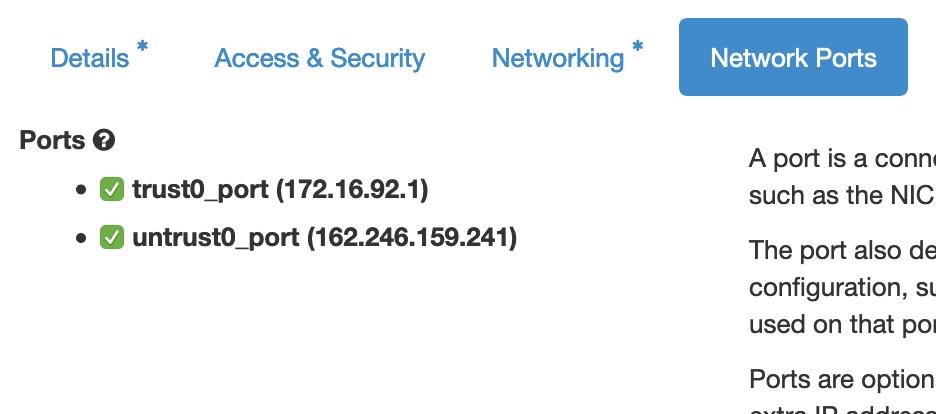
The ports will be added to the firewall and will appear in the firewall's operating system in alphabetical order. This means that the If you are importing an existing firewall configuration, you might have to rewrite the configuration or reconfigure your firewall to change the order of the ports accordingly. |
At this point your VFS instance is ready. You can then use a VPN to connect to it and then either SSH using the default management IP, or open a web browser and add “https://<default IP> and then hit enter. See the Access and Maintenance of Your Virtual Firewall section.
For fortigate VMs launched from FortiOS image version 7.x, management access through http is not allowed by default, as was the case for earlier versions. As such, additional configuration via SSH is required before the web GUI is accessible. Make sure your RAC VPN is connected, and do the change as follows:
Once this is done, you can go ahead and access the fortigate web GUI. |
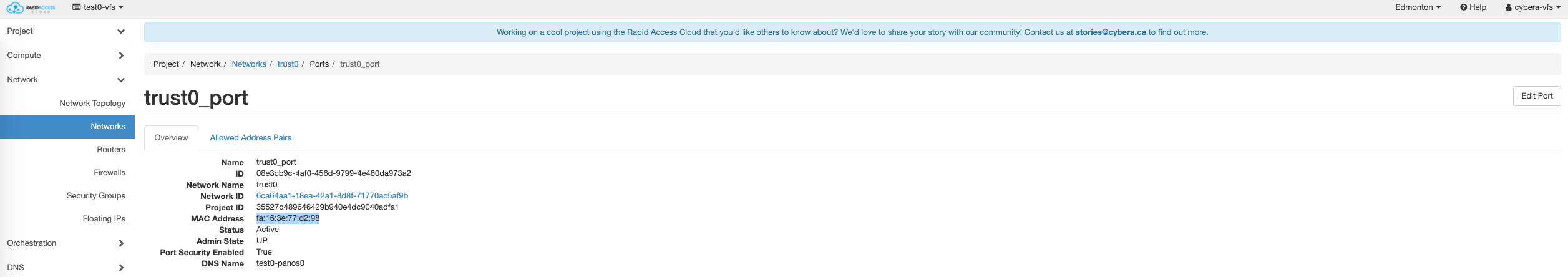
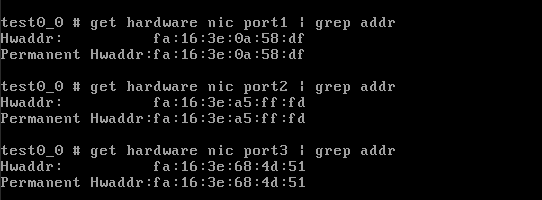
Take note of the trust0 and untrust0 MAC addresses from the cloud side, using RAC portal (horizon) as shown in the example below
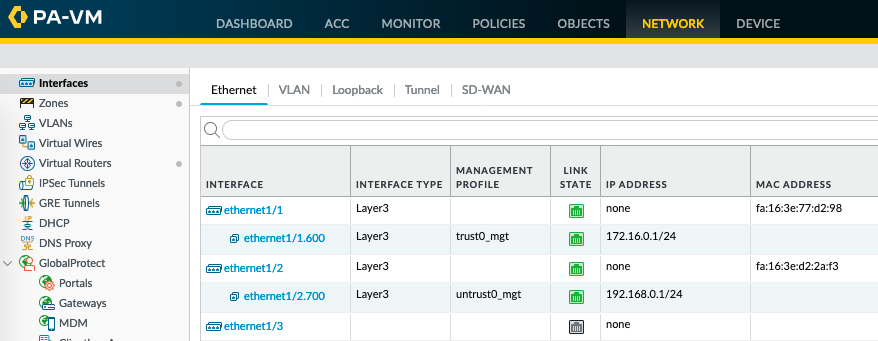
Command line (using horizon instance console or ssh to instance)
admin@PA-VM> show interface all total configured hardware interfaces: 2 name id speed/duplex/state mac address -------------------------------------------------------------------------------- ethernet1/1 16 10000/full/up fa:16:3e:77:d2:98 ethernet1/2 17 10000/full/up fa:16:3e:d2:2a:f3 |
The Virtual Firewall Service (VFS) is intended as a self-managed service, and Cybera does not perform backups of your firewall configuration.
See the How to Make a Backup of Your Virtual Firewall Configuration section for more details.
During a failover scenario, having at hand a copy of your firewall configuration will ensure that the service is restored in a timely manner. See the Handling Outages section for more information.
We recommend you to keep at hand a copy of your firewall authorization code (authcode), if you are a Palo Alto firewall user, or a copy of your license file, if you are a FortiGate firewall user. For more information on how to activate your firewall license, please see the section How to Activate Your Firewall License.
For Fortigate firewalls, if you are using the "FortiToken" functionality, then consult with Fortinet Support for the steps to re-host your FortiTokens. FortiToken keys are not transferred as part of the configuration backup and require involvement from Fortinet TAC to re-host on a new installation.
The Rapid Access Cloud dashboard can be used to delete a firewall instance, in case a given firewall needs to be re-launched or recreated: One scenario where this might be required is a failover event, see for instance the Handling Outages section.
Before deleting a firewall instance:
|
Once you have a backup copy of the firewall configuration and you have delicensed the firewall if you are using a Palo Alto firewall, follow the steps below to proceed:
Login to Rapid Access Cloud by choosing the correct region where your firewall is running;
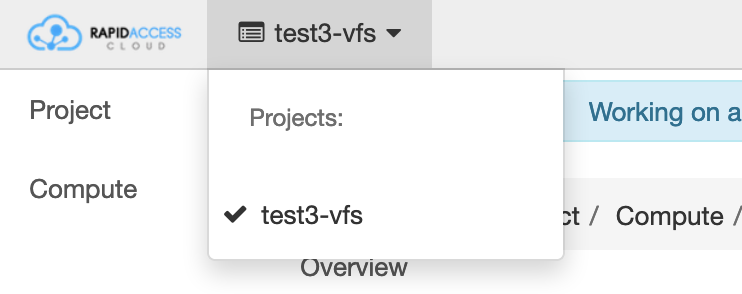
Change the project to the vfs project at the top left corner (see Step 2 in the Launching a VFS Instance section above);
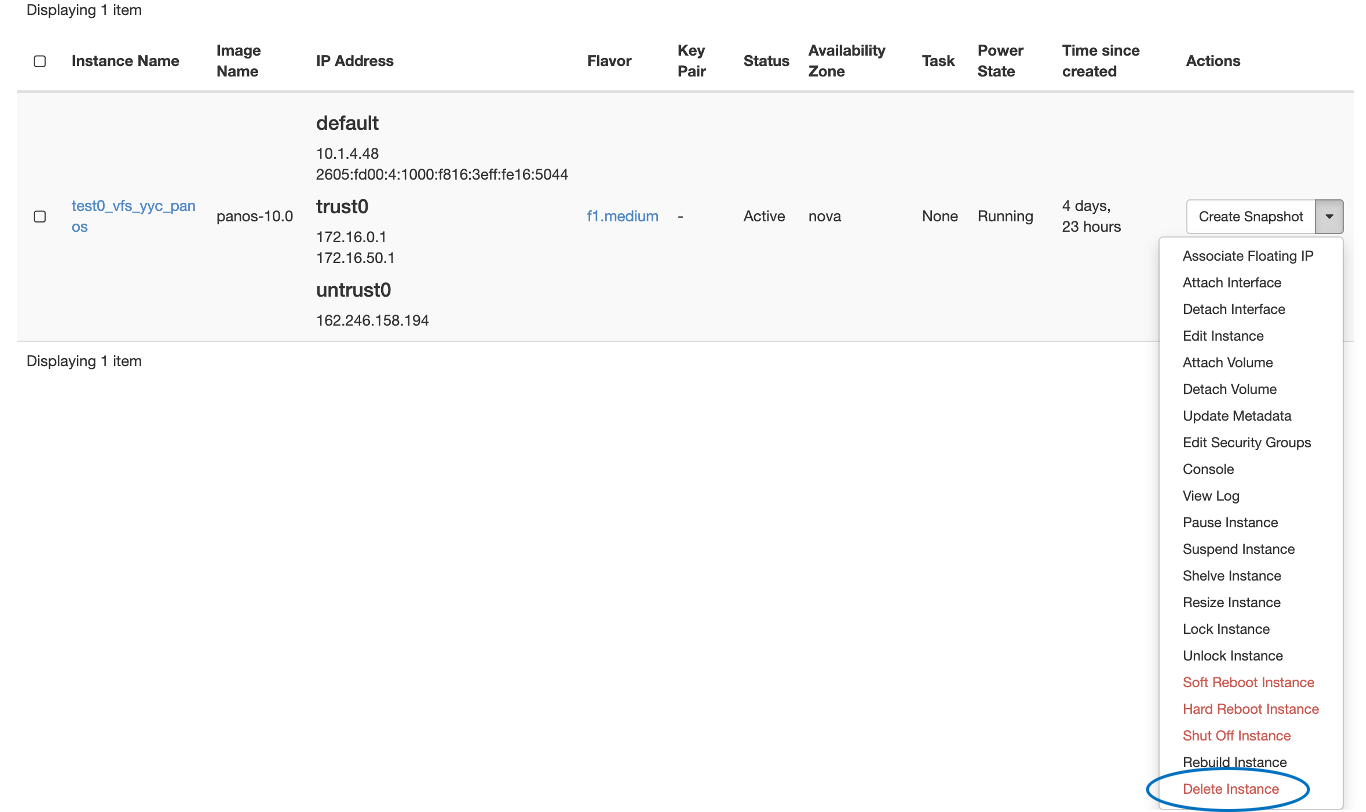
Click on “Compute”, and then on “Instances”, and from the instance Actions menu, choose “Delete Instance”, as shown below: